5G isn’t the next step up the staircase… it’s a leap from landing to landing. And as we delve deeper into the era of digital transformation, the advent of 5G technology stands as a pivotal milestone. The revolutionary network technology is not just an upgrade in speed — it’s a gateway to a realm of new possibilities for business technology. … Read More
Why Your Employment Agreement Needs a Technology Clause
In the ever-accelerating era of technology, companies today are the unwitting custodians of vast digital fortresses. These fortresses— stocked with trade secrets, personal customer information, financial data, etc. —have become a veritable treasure trove for cyber-thieves. And it’s not only the rogues lurking in the murky waters of the internet you need to worry about; more often than not, the … Read More
Leverage’s best of 2022
2022 has been a crazy year on several fronts — re-opening the country post-covid, a new normal for work, rampant inflation, war in Ukraine… it’s been a lot. The same is true for businesses as we navigate an ever-more hostile security environment, a constant need to innovate and upgrade our tech stacks to keep pace, etc. Leverage has been publishing … Read More
How to move your business from ‘respond’ to ‘recover’ post-Covid
Are we starting month 7 or month 70 post-pandemic outbreak? It feels like it was only yesterday and a lifetime ago that WFH became the new normal. And while there are a litany of problems facing us as individuals and as society, business problems are also core to the recovery. Without an economic recovery, there is no actual recovery. As … Read More
Has CoVid proven asynchronous video messaging is enterprise ready?
CoVid-19 has upended, well, pretty much everything. There’s a decade’s worth of reading on all the ways it has impacted our lives, both large and small; there will be more to come. That said, not everything it has revealed or impacted is necessarily bad — those favoring flexible working arrangements now have ample evidence it really can be done at … Read More
Why IT stability is the mother of productivity (and how to get it)
Labor productivity is higher than it has ever been before. This is great news for business owners as well as for retail investors, because it means the American economy is growing overall. Many things contribute to these productivity gains, from better workplace management and collaboration tools to the overarching influx of technology that simplifies tasks, automates repetition, and massively increases … Read More
WhatsApp vulnerability threatens billions of users—what you need to know
WhatsApp promises users end-to-end messaging encryption, but the app has a massive vulnerability. What your business needs to know, and lessons to learn:
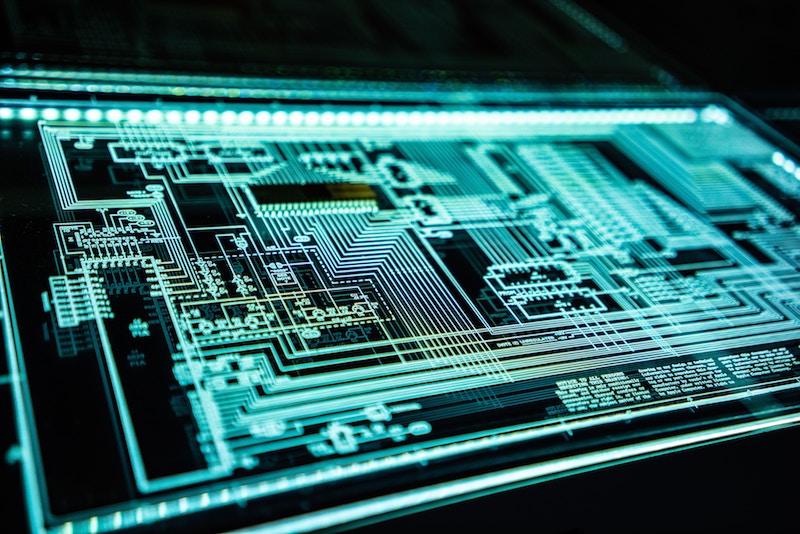
iSCSI vulnerability reveals another avenue hackers are exploiting
There’s seemingly no end to the avenues for hackers to penetrate protected systems. From simple (yet dishearteningly still effective) email phishing to DDoS overloads to high-complexity malware/ransomware custom-built for specific targets, hackers are becoming ever more effective and creative in gaining access to sensitive systems. But the first line of defense is still your employees, and in a recent snafu, … Read More
The skinny on LockerGoga, a terrifying new ransomware variant
We’ve seen all manner of ransomware in the last decade. From innocuous varieties to the devastating ones, ransomware is one of the largest (and growing) threat vectors for cybersecurity teams (or managed service providers if you outsource that sort of thing). One of the newest iterations on the scene, with a terrifying wrinkle, is called ‘LockerGoga’ — here’s what it … Read More
Triton is the rare malware that can cause physical harm (and even death)
When we think of cyberattacks, we tend to think in digital terms. It’s typically digital tools that gain access to digital systems that hackers then use to their assorted nefarious ends — whether that be ransom, blackmail or anarchic destruction. Often the data stolen is digital itself, the demands are presented digitally, and if assets of one kind or another … Read More




Dive straight into the feedback!Login below and you can start commenting using your own user instantly