As the CEO of Leverage, the premier Managed Service Provider (MSP) in DFW, I’ve always been committed to the proactive adoption and adaptation of new technologies that drive our clients’ success. Today, I’d like to share some insights about one of the most influential trends shaping the modern business landscape: remote work, and the crucial role MSPs like ours play … Read More
How the news endangers your company’s security
The news media catches a lot of heat for a lot of different reasons. Much of that is justified, some of it not so much. But regardless of where you fall on that particular ideological spectrum, if you own a business, the news can be a huge threat to your cybersecurity and IT reliability. Wait… what? I know, I know. … Read More
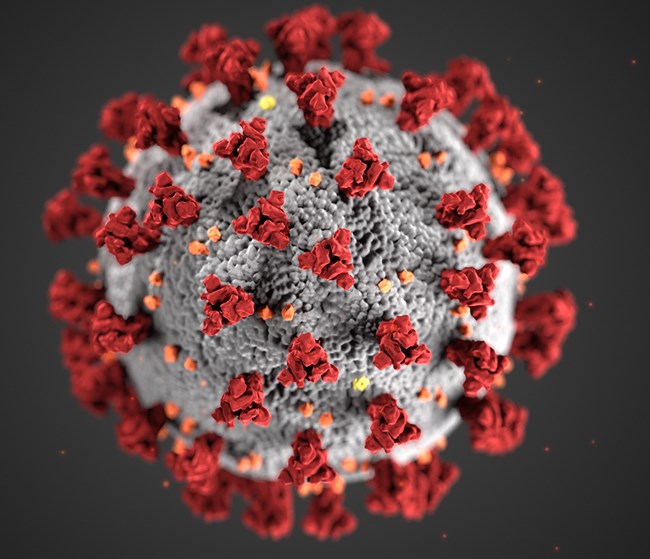
CoVid-19 phishing scams are on the rise — what to know
No event in living memory (unless you’re 106 years old) has impacted daily life across the globe as completely and deleteriously as CoVid-19. The coronavirus and its disease have upended every facet of daily life for basically everyone in this country. Every child is home schooled now; every office is at home unless you’re an essential worker (our thoughts, thanks … Read More
Coronavirus stress tests businesses’ digital infrastructures in real time
First and foremost, we want to extend our sincerest well wishes to the countries, states and cities battling the ravages of the Coronavirus pandemic. The health and safety of our fellow humans is the most important thing right now — so heed the advice/directives from CDC and WHO, let’s start keeping some social distance, and for god’s sake, wash your … Read More
How OpenDXL Ontology could change your technology stack
One of the most common subjects on this blog is cybersecurity. It’s by no means all we do as a managed IT provider; but, when your #1 goal is uninterrupted uptime for your clients, security breaches rank pretty high on the list of things we have to watch out for. It’s also the space within our industry that sees the … Read More
7 Best Specialist Solutions IT Support Firms Offer
When you first take over the reins of a new business or are trying to bring your long-standing one up to a modern standard; it can be like learning to walk. Technology is changing at a rapid pace, and a new system without expertise or knowledge to run it can seem like a nearly impossible undertaking. It can feel like … Read More
Top 5 Ways Managed IT Service Plans Can Save Your Business Money
In a competitive business world, every manager or owner has to think outside the square to make savings. Profit margins are getting slimmer by the day, and there’s only so many cuts you can make until you’re operating on a shoestring budget. That’s where a managed IT service plan from a reputable firm can be a gamechanger. It benefits almost … Read More
Why You Should Outsource Your Business’ IT Support
For many small and medium-sized businesses, there comes a time when IT problems take over your working week. You can spend more time trying to troubleshoot and maintain your systems than you do on your own job. At that point, you have to ask yourself: should I be outsourcing my Business IT? The answer might be yes. Read on to … Read More
Getting our clients back to work after severe weather wracks Texas
The last thing you want to worry about when severe weather strikes is your company’s data—here’s how we got our clients back to work with minimal downtime.
WhatsApp vulnerability threatens billions of users—what you need to know
WhatsApp promises users end-to-end messaging encryption, but the app has a massive vulnerability. What your business needs to know, and lessons to learn:







Dive straight into the feedback!Login below and you can start commenting using your own user instantly