There might never have been such a ripe time to experience professional burnout. We’re rounding the corner into Year 3 of a global pandemic; we’ve spent much of the last two years in some form of lockdown, juggling a new working reality all while figuring out child care, education, you name it… add in trying to maintain some semblance of … Read More
How Russian cyber weapons could impact your business
Russia’s recent invasion of Ukraine is far from the first time Russia has exhibited hostilities toward Ukraine. Beyond the annexation of Crimea in 2014, Russia has been practicing and perfecting its cyber arsenal using Ukraine as a training ground for years. From physical infrastructure system attacks (like on Ukraine’s power grid), to devastatingly simple rogue worms that escape Ukraine’s borders … Read More
Data integrity: just as important as data security (but not the same)
We’re on a bit of a kick to define important terms in businesses’ approach to technology. Last month it was IT management vs cybersecurity management. Why are we defining things like IT management, cybersecurity management, data integrity and data security? Because properly framing the conversations around each can have profound impacts on how businesses can correctly approach these disciplines. In … Read More
Cyber insurance: why you need it, what it takes to qualify
We’ve written time and time again about protecting your company and its assets from cyber attacks. Threat vectors are multiplying in both form and function while the rise of ransomware-as-a-service should give any business leader nightmares for how accessible it makes carrying out sophisticated cyberattacks to would-be hackers. So what do you do? How do you protect yourself against downside … Read More
IT management vs cybersecurity
IT management and cybersecurity go hand in hand. There are few companies in 2022 that can be successful without high-level performance on both fronts. For most small and medium-sized businesses, these may not even be treated as separate functions or departments, but rather lumped together into the “technology” bucket (which isn’t exactly wrong, either). But, there are important distinctions between … Read More
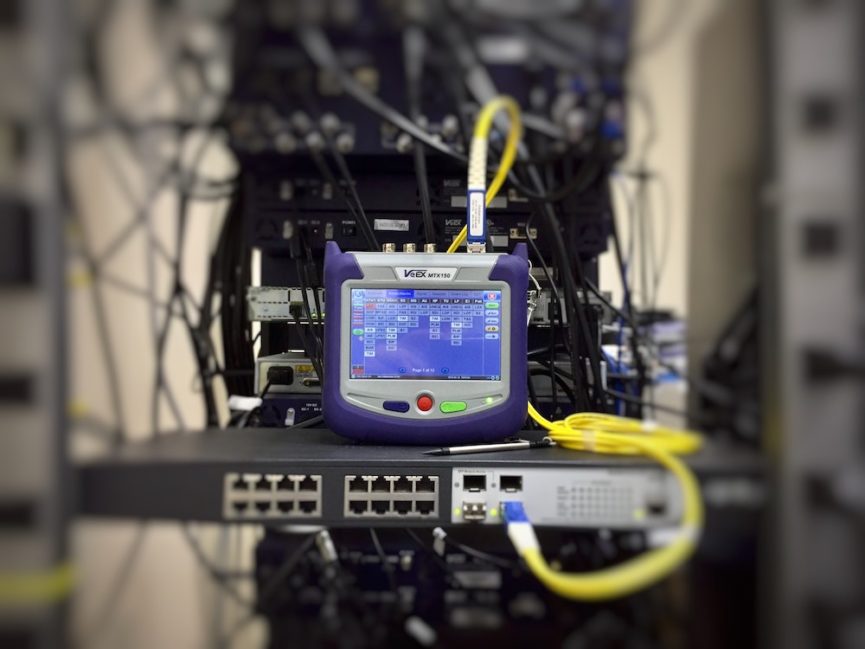
Critical Apache Log4j vulnerability — what you need to know
Every week it seems, the public finds out about a critical piece of digital infrastructure that’s providing an unwitting vulnerability for hackers to exploit. Unless you’re a CIO or work in cybersecurity/risk mitigation, you may not even know how integral some of these systems are when the vulnerabilities are disclosed. That might be true for the most recent high-profile announcement … Read More
Ransomware (mostly) isn’t costly because of the ransom
When you think about ransomware, I have to imagine you envision the ignominy of paying millions of dollars out of pocket to get access to your data back. The scary part is right there in the name: ransomware. The ransom is the nightmare scenario. While there is certainly a built-in, deep-seeded personal affront to being the victim of a ransom … Read More
Microsoft Power apps misconfiguration exposes 38MM sensitive records
Not every major data breach or cybersecurity incident is the work of master hackers with government-level resources and support. As we’ve discussed here before, ransomware as a service is a large and growing threat to small and medium-sized businesses the country over. But, it’s not always nefarious actors who are deliberately targeting you that you have to worry about — … Read More
The ransomware protection checklist
The Cybersecurity and Infrastructure Security Agency (CISA) recently released a detailed report about the ransomware-du-jour, BlackMatter. Similar to other Ransomware-as-a-Service threat vectors (which we’ve written about before), it’s cheap and easy to deploy, utterly devastating to infected systems, and cause for real concern in the IT community. I wish this wasn’t such a tired story, but this is life in … Read More
How SIEM can protect your business from cyberattacks
There really is no way to overstate the cyberthreat environment small and medium-sized businesses find themselves in today. Attacks are up across the board (and not just for large enterprises). The tools hackers are using are both more advanced and more pernicious… all while being more widely available. Now, this shouldn’t come as that big of a surprise to anyone … Read More







Dive straight into the feedback!Login below and you can start commenting using your own user instantly