If it hadn’t been for Somali pirates, Navy Seals or the Tom Hanks movie Captain Phillips, chances are you probably wouldn’t have heard of A.P. Moller–Maersk Group, or ‘Maersk’ for short. It’s one of those companies content to work in the background, unnoticed and unknown, while at the same time fueling the entire world economy. It’s one of the largest intermodal logistics … Read More
Chinese spies used a microchip to infiltrate 30+ American tech giants… here’s what you need to know
Last week, Bloomberg Businessweek dropped the bombshell of all bombshells when it comes to cybersecurity. Everyone knows hackers are an ever-present danger in our digital lives — whether its phishing attacks, DDoS attacks, WiFi attacks, whatever — we’re always having to be on the lookout for suspicious activity throughout our digital lives. But a legit and systemic hardware attack? That’s another … Read More
Why hackers target you through IoT, how to spot a breach and how to protect yourself
In our most recent post, I walked you through the promise of the Internet of Things (IoT) from a consumer perspective before relaying a seemingly crazy anecdote about the increasingly creative (and nefarious) ways hackers are using IoT devices as access points to otherwise secure networks safeguarding sensitive data. It’s an important first step — recognizing IoT as the vulnerability … Read More
IoT does some pretty awesome stuff… and opens you up to all kinds of risk
The Internet of Things (IoT) has been on the horizon for years — in some ways, decades even. From fictional depictions as far back as the Jetsons to the promise of a smart home with intuitive tech that not only responds to your every command but can anticipate all your needs, it’s been a tantalizing frontier in consumer electronics for … Read More
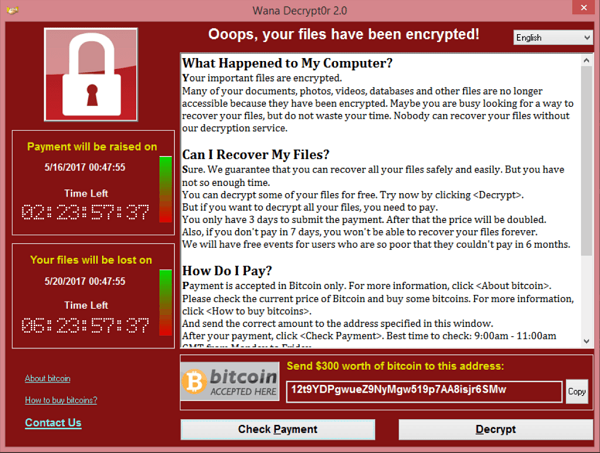
Ransomware is a huge and growing problem — here’s 4 ways to protect your business
All the trend lines point one direction when it comes to ransomware frequency and scope of damage — up and to the right. A report from Cybersecurity Ventures projects that on average, there will be a ransomware attack on a business every 14 seconds by the end of 2019 — up from a rate of one attack every 40 seconds … Read More
Intel Announces Major Security Breach
You’ve probably seen or heard about the massive security vulnerability Intel announced last week. This recent acknowledgement has the potential to dwarf the WannaCry attacks from 2017 when you consider the combined impact of attacks and performance loss. Intel Security Breach The vulnerability is at the heart of the processor architecture. This issue applies to the last 20+ years of processors … Read More
The Cloud is NOT for Everyone
The cloud concept has a lot of momentum lately, but it’s not the right solution for everyone. So what determines if the cloud is right for you? There are a few key characteristics of your business that will push you towards a cloud implementation. How far you go is determined by your need for those characteristics. The important thing to … Read More
The Leverage Service Experience
The Leverage Service Experience is unique. It’s like the feeling you get when you go home for Thanksgiving. You don’t use it everyday, but when you do it feels comfortable and familiar. The person you talk to knows who you are and what you like. They know how you like to be treated and how you want your computer to … Read More
9.5 Remote Worker Requirements
More people than ever are working away from the office. The modern employee expects the ability to perform her entire list of job duties from anywhere. As an employer, it’s a competitive advantage in your market for acquiring business and top talent. As with any new technology it comes with some risks. You must account for the security requirements first … Read More
How to Fire Your IT Company
Have you ever broken up with your IT company? The process can be messy. In a perfect world you get your passwords without issue. Your backups are provided on the exact day you ask for them. All services are retained under your company name and your former IT provider is removed as an authorized contact. But the world isn’t perfect. … Read More




Dive straight into the feedback!Login below and you can start commenting using your own user instantly